To the Experts Corner
Ship to Shore: How to Face Growing Cyber Threats
How are growing cyber threats changing ship-to-shore emergency preparedness?
Cyber threats are everywhere these days, but few sectors have been as hard hit as maritime shipping. In 2025, cyber incidents surged 103%, and these attacks are no longer confined to shore-side systems. They often target operational technology on board — navigation, engine monitoring, communications — and even the link between vessel and shore itself.
Regulatory frameworks are tightening, with new requirements on controls and incident reporting now coming into effect across multiple jurisdictions. In this context, a few recent incidents got me thinking about what resilience requires now from emergency preparedness.
A crew working from a false picture
In May 2025, the MSC Antonia ran aground in the Red Sea. Investigators linked the incident to GPS spoofing — manipulated satellite signals that fed the vessel's navigation systems false positioning data. The crew was making decisions based on information that wasn't real.
This is not an isolated case. GPS and GNSS spoofing in geopolitically sensitive regions — the Persian Gulf, the Black Sea, the Eastern Mediterranean — is a well-documented and growing threat. In late 2023, over 100 cargo ships suddenly appeared on AIS tracking systems to be located at Beirut airport. In the Gulf, spoofing has been used specifically to manipulate vessel position data, creating a false pretext for interception.
Snorre Halvorsen, who leads loss prevention and emergency response at Norwegian Hull Club, raised this directly in a recent webinar: a collision in Turkish waters where the vessel's AIS signal had been spoofed, and the crew — trusting what their systems told them — weren't looking at the radar or even out the window. They relied on inaccurate information and worked from a false picture of the world.
What the regulations say
Whether it's IMO, NIS2, or the US Coast Guard, the message is increasingly the same: it's no longer enough to recover from an incident. You need to be able to show how it was managed.
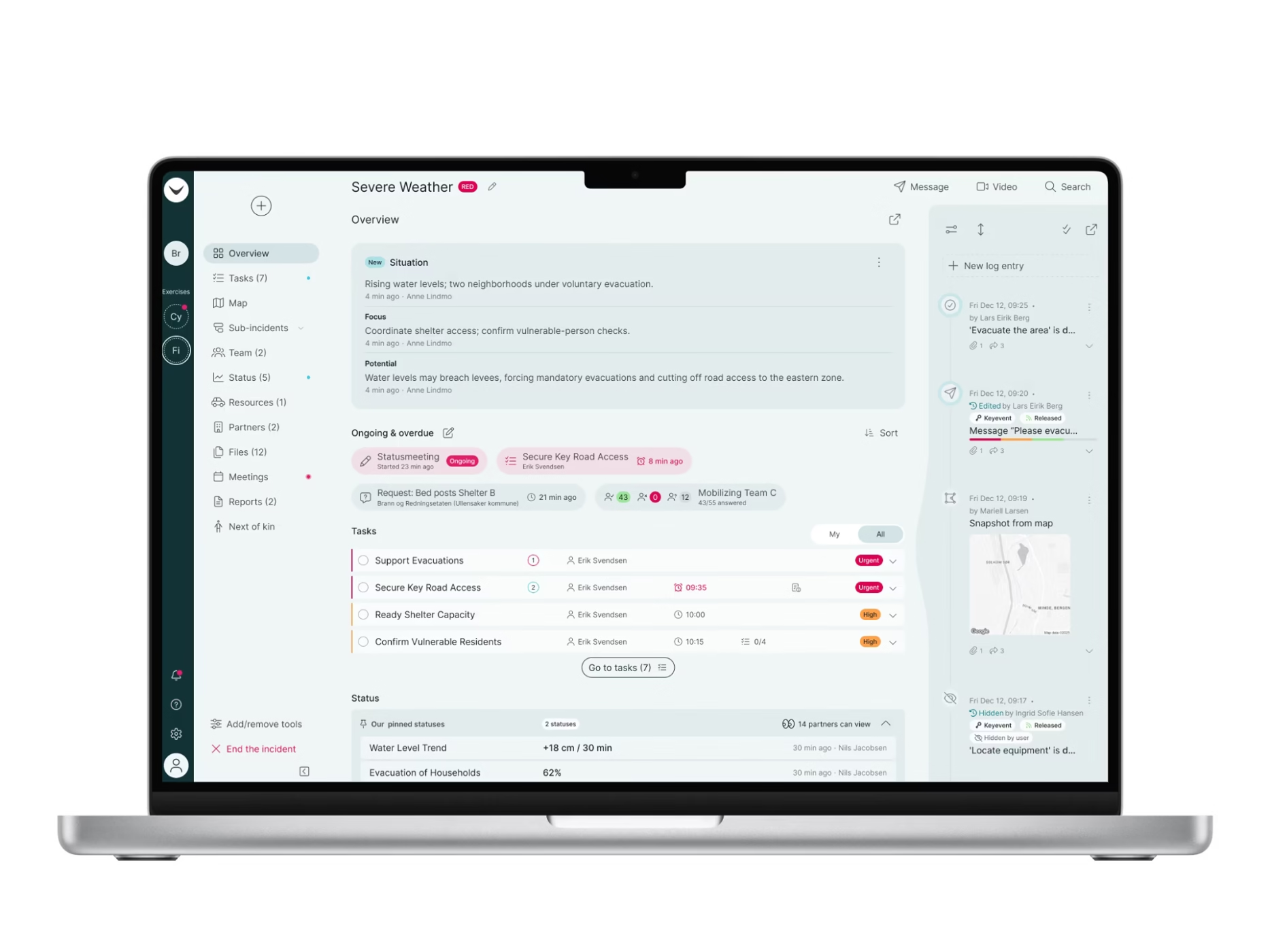
This means shifting from compliance as a defensive posture to resilience as an operational requirement. Cyber risk and resiliency today depend on fully coordinated emergency preparedness and incident management capabilities that work even when systems are targeted and organisational networks taken down.
Cyber resilience from ship-to-shore
Let me offer an example. In two waves in 2025, attackers targeted Iranian vessels through a compromised satellite communications provider, cutting the operational link between around 180 ships and their shore teams. The modems were physically destroyed. Crews were still at sea. Shore teams had lost the connection entirely.
Such a scenario makes the ship-to-shore question impossible to set aside. The shore-side hotline model — a vessel calls in, someone experienced picks up, the response unfolds from land — assumes that the vessel can call. It assumes the information coming through is reliable. But as real-world examples show, a cyber incident can sabotage the very infrastructure needed to communicate and create accurate situational awareness.
When a cyber incident strikes, organisations still need to coordinate and communicate while generating a record of the response as it unfolds. Regulators, insurers, and investigators will ask. After an incident, organisations need to be able to demonstrate:
- how it was managed — in sequence, under pressure, and across the organisation
- what was decided, and on what basis
- what was communicated from ship-to-shore
- what actions were taken.
If that record does not exist in time-stamped logs, it has to be reconstructed later based on multiple accounts and memories. This is when incident management starts to look more like guesswork.
Cyber resilience — the ability to anticipate, absorb, respond to and recover from attack — depends on both the technology and the organisational capability to keep operating when systems are under pressure. That means having a record of what happened, one that supports the review and continuous improvement that follows every incident. For maritime shipping, the stakes are clear: the safety of the crew, the vessel, and the wider sector depends on getting it right.
Pro tip
Emergency preparedness capability should not depend on the same organisational network most likely to be compromised during a cyber incident.
Read more from the "Ship to Shore" series
Talk to a RAYVN Expert
Don't just test a tool—optimize your strategy. Sit down with a RAYVN expert to verify our features meet your compliance needs and see how easy it is to manage complex incidents in real-time.